Relaying Hashes from Responder

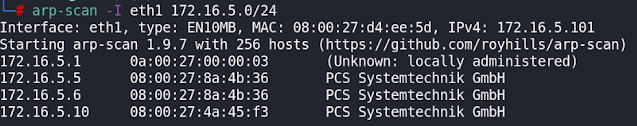
In this lab, I captured a hash using Responder, and then relayed it back to the same machine to open a shell. This shell was then upgraded and via pivoting a new machine was exploited. To start with, I did a scan to find open ports on the target machine. Next, I did a more thorough scan of the discovered open ports. I found that the remote machine was using netbios and running Windows 7. The remote machine was running x86 architecture (32 bit) so I had to remove the original x86-64 (64 bit) files from the relay tool before compiling 32 bit versions. I then turned the responder http and smb servers off as I wanted to relay the captured hashes. This was achieved by editing the file found @ /etc/responder/Responder.conf I then started the Responder and Multirelay tools. An ntlmv2 hash was captured and relayed to open an interactive shell. From this shell, I was able to ascertain that the remote machine was connected to a second subnet (10.100.40.0/24) In order to upgrade this shell ...